Do I Need a VPN? Their Uses Explained
VPNs (Virtual Private Networks) are an increasingly important and widely used security tool. What was once a fairly obscure technical term has now practically become a household name. This unfortunately means that it has also become a buzzword for those who may not have your best interests in mind. This article seeks to empower anyone considering a VPN with the basic essential knowledge about how they work and where they are ideally used.
Contents
VPN Uses
The effective purpose of a VPN is to connect your device to a remote network via an encrypted tunnel. There are many technical details about how they work, but those are not within the scope of this article. Using a VPN is functionally similar to physically plugging your device into the same remote network with a really long network cable. The reasons for using a VPN generally fall under 3 categories:
1. Access
To securely connect to systems and resources on a remote network.
This can likely be considered the original intended purpose of a VPN, and has become ever more widespread with the Covid-19 pandemic and resulting increase in remote work. Instead of opening up firewall ports to applications and inviting the obvious resulting security risks, a company can allow authorized remote users to connect to the network via a VPN. This simplifies management and increases security by routing all applications and protocols over a single encrypted connection. A VPN can also be set up on a home network; or really any network that you control. Entire remote networks can even be connected together over the internet using a VPN.
2. Disguise/Mobility
To change your public IP address and the exit point from which you access the internet.
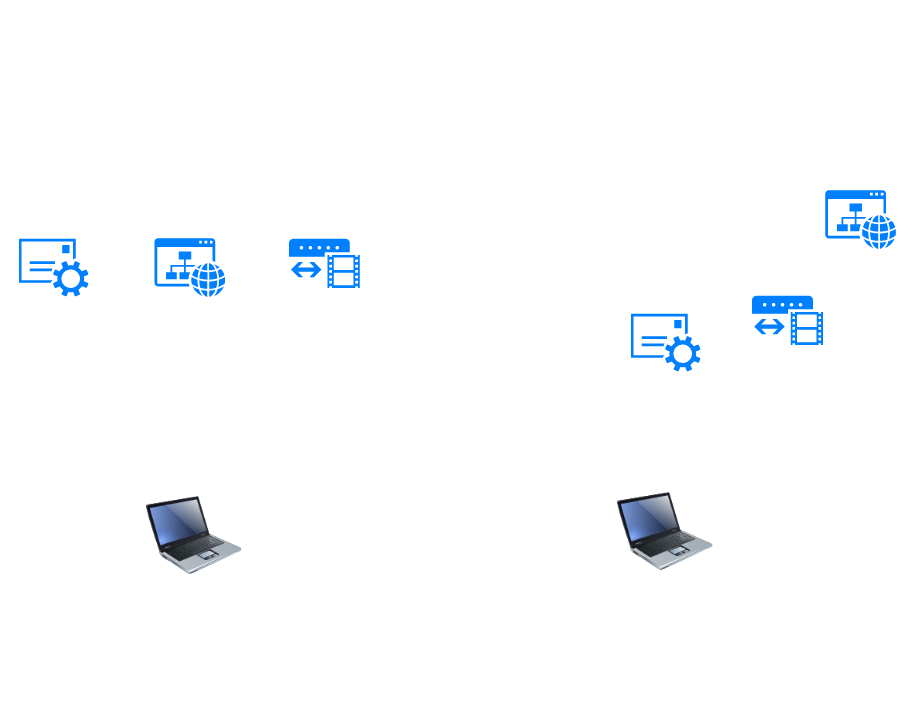
This is likely the most popular use for VPNs among average users. When accessing a website or service on the internet, the public IP address of the network you are currently attached to is visible to any websites or services you visit, and can be subject to restrictions based on the geographical location and/or other factors related to that address. When connected to a VPN, your public IP address/exit point becomes the public IP of the network your VPN client is connected to. Many paid VPN services now operate networks in locations all over the world, and allow you to choose the location you wish to connect to.
3. Privacy
To encrypt personal network traffic against eavesdroppers.
Since a VPN effectively tunnels all of your network traffic over a single encrypted connection, it can be used to comprehensively ensure that all of that traffic is secured against eavesdroppers. Depending on the websites you visit and applications you use, the individual connections to most of them may already be encrypted, but being connected to a VPN means that all traffic is sent over a single encrypted tunnel that cannot be read by anyone between your device and the network your VPN client is connected to. Whether and when this is necessary is explored in the next section.
Do I need a VPN for Privacy?
One of the biggest selling points marketed by paid VPNs is to “protect your privacy”. A VPN can indeed be used as a tool for this purpose, but it is important to understand the use cases as well as the limitations. In the past it was common for most web traffic to be sent unencrypted. Encrypted protocols such as SSL/TLS were only used for particularly sensitive communications such as credit card transactions and accessing bank accounts; leaving everything else to be easily eavesdropped on. In today’s security-conscious world, however, it is standard for almost every website and application to use encrypted protocols.
So do you still need a VPN to protect your privacy? This depends on the situation.
On the Go
Using a VPN is generally a wise practice when connected to the internet outside of your work or home network, such as the WiFi at a coffee shop or hotel. Even if you trust the owners of said network, they cannot account for everyone else who may be on it. Being connected to a trusted network may also allow you to take advantage of any security tools that are set up there, such as web filters.
As stated earlier, most modern day websites and applications are already encrypted, so there is very little chance that your credit card information or conversations on a messaging app will be stolen as the result of connecting to an insecure network. However, someone monitoring your activity would still be able to see which websites you are visiting and what apps you are using, which could potentially reveal a lot about you. There is also the possibility that one of these websites or apps could have poorly implemented security or undisclosed vulnerabilities that could be exploited. Tunneling all of your traffic over a secure VPN reduces or eliminates these potential issues.
From Home
One would think the safest place to use the internet is from your own home, as the only other party who can see your home internet traffic is your ISP (Internet Service Provider). Unless you are doing something technically illegal, there should be no reason to hide your public IP or encrypt all of your traffic, right? Unfortunately even your ISP may not have your best interests in mind. In the U.S. they are legally allowed to sell customer browsing history to 3rd parties without your explicit approval; a right which many of the largest providers lobbied for.
Using a VPN is certainly one way to protect your privacy from your ISP, however it is not an ideal method and there are some potential disadvantages to consider. Being connected to a VPN often comes with a performance cost, and you may see decreased bandwidth and increased latency on your connection. Also see below for potential caveats of paid VPN services.
A better practice for protecting your browsing history at home is to use DNS encryption. I will cover this in a later article.
VPN Options/Trust
So what option should you use for a VPN? This depends on what purpose(s) you intend to use it for. Fortunately VPNs are an open concept, and most services make use of established standards and protocols, as well as open source software.
Self-Hosted Home/Business VPN
A VPN server can be configured on any network that you control, such as a home or business network. Larger businesses with a need to provide access to many users will typically buy commercial software – from a vendor such as Cisco or Fortinet – that will provide more management features and easier setup. For small business or home use, some feature-rich network routers often come with an integrated VPN feature that can be enabled. There is also the option to create a VPN server using freely available open source software such as OpenVPN or WireGuard. Such software is often used at the core of commercial VPN software or a router’s integrated VPN, and typically takes more technical expertise to set up from scratch. There are many tutorials for doing so available on the web, and even automated setup options, such as PiVPN, that streamline the process.
Paid VPN Service
Paid VPN services such as ExpressVPN or NordVPN are widely advertised, and are the simplest option for being able to mask your IP and connect to various locations around the world. They are often marketed as a form of security and privacy protection, but there are caveats to keep in mind when using them:
- The popularity of VPNs means that there are many less-than-trustworthy companies operating paid services. Some may operate insecure networks, include vulnerabilities or even malware in their applications, and/or abuse your personal data. It is important to use a service that is reputable.
- When connected to a VPN service, they have visibility into your unencrypted traffic. Many providers claim not to retain any logs about their customers’ activities, but evidence to the contrary has been found in some cases. Always remember that a VPN does not universally hide the visibility of your network traffic, but simply moves it to the network it is connected to.
- Using a paid VPN service also means sharing an exit node (and its public IP address) with many other users. It is all but guaranteed that the same node will see a lot of shady activity emerging from it, and many sites will place restrictions on that IP as a result. I have encountered many more Captcha requirements while using a paid VPN service, as well as some websites and services that refuse to connect; likely because the IP has been banned.